What’s going on in China? I was invited there for a series of lectures at Beijing’s Communication University of China (CUC) during the week of March 18. Thanks to Professor Xu Peixi, who organized the tour, I got a chance to meet most of the academics, researchers and policy analysts involved in Internet governance in Beijing think tanks, as well as many students. There were also some discussions with Chinese Internet businesses and a lecture at Tsinghua University’s Journalism and Communication Department. By coincidence the visit occurred shortly after the conclusion of the National Peoples’ Congress, and overlapped with news of the Facebook breach and President Trump’s Section 301 actions against China. As China threatened tariffs of its own, the U.S. stock market plummeted in anticipation of the damage of a US-China trade war. While most of the news was not good, it was certainly an “interesting time” to engage in discussions of Internet governance and U.S.-China relations in cyberspace.
Multistakeholder, multilateral, multiparty
Many in the Chinese government are still coming to terms with the concept of multistakeholder governance. As noted above, China participates actively in institutions such as ICANN, while at the same time officially favoring multilateralism in UN forums. Asked by government officials whether it was possible to find some middle ground between multistakeholder and multilateral governance, I said that it was not; we need to recognize them as distinct and mutually exclusive forms of governance in any given sector. Any attempt to bring about a mixture of the two was likely to be messy and dysfunctional. A better approach is to confine multilateral governance to areas where it cannot be avoided, such as in military or trade negotiations, while allowing nonstate actors involved in multi-stakeholder governance the ability to function authoritatively in areas requiring global coordination, transnational operations and broader representation. Another question asked whether multistakeholder governance is unrealistic because not all stakeholders can have equal representation. I replied that nonstate actor-based governance is valuable not because it provides perfect representation of every sector in society, but because it allows anyone with knowledge and commitment to be heard. That openness better leverages the knowledge latent in the community, and does a better job of incorporating diverse views. Multilateral governance, in contrast, eliminates everyone but governments. Multistakeholder governance is therefore more likely to incorporate viewpoints and knowledge that will be needed to develop and understand the effects of policies.
The idea of governance rooted in transnational non-state actors (which is a more accurate term than “multi-stakeholder”) seems to be gaining ground in China. I met the private sector founders of a new organization, the Multi-stakeholder Forum for a Better Cyberspace, which was recently incorporated in Beijing. In contrast, comments made by a member of an official think tank after one of my talks mentioned “multi-party” governance as to suggest some kind of a synthesis or middle ground between multilateral and multi-stakeholder. To some, this may sound like official China is edging towards multistakeholderism. But a close observer of China should wince at the term “multi-party.” As this article from one of China’s external propaganda outlets shows, official China uses the term “multi-party cooperation system” to describe its own political system – described as a “cooperation system” in which the Communist Party of China holds power and eight other democratic parties participate in state affairs in a purely consultative role. “Unlike the two-party or multi-party competition systems of Western countries, the multi-party cooperation system has endowed China with the advantages of long-term planning and the integration of resources, thus enabling it to solve complex problems and further reforms.” So in IG terms, I would guess that “multi-party” means a state-led system in which civil society and business are present but relegated to consultative roles. Well, I must admit that in some of the darker moments of ICANN’s history, its multistakeholder model had a lot in common with the Chinese multi-party approach.
Fussing over CFIUS
Some of my discussants were only vaguely aware of the Committee on Foreign Investment in the U.S. (CFIUS) but they are beginning to hear more about it – and ask about it – after its role in blocking the Ant Financial-Moneygram and Broadcom-Qualcomm deals. It should be noted that all of the leading Internet companies in China are private enterprises. While heavily regulated they behave like competitive firms, often chafe at regulation, and are interested in expanding their markets and profits. One group inquired about a Senate bill that would broaden the scope of CFIUS reviews (known as FIRMMA). I said that FIRMMA was a bad idea, and that its authors were deeply confused about the proper boundary line between national security and industrial policy. It interjects national security concerns into a much broader swath of the economy. In this case, the Chinese and I agreed readily that the bill is being proposed by representatives who want to target China for discriminatory investment barriers in a broader set of high-tech areas. It would be hypocritical for the US to continue to complain about how China erects trade barriers in the name of national security while moving the in same direction itself. Asked how we can overcome barriers to FDI between US and China, I heard repeatedly that we need to get rid of a “cold war mentality” and a “zero sum game approach.” Trump’s Section 301 action is an example of zero sum game, they said: “the US side ignores our voice and is unwilling to talk.” While it’s true some American companies are blocked from entering the China market, Chinese civil society is said to complain that Huawei can’t sell in America but Chinese can buy Apple devices here.
ICANN and the DNS root
ICANN and the DNS root continue to be topics of interest in China. I was asked about how China contributed to ICANN’s reform, and how could China contribute in the future. I explained that China was present and well-represented during the IANA transition and ICANN reform process, and that the rest of the community appreciated this. People like Li Xiaodong (formerly head of CNNIC and now at Tsinghua University) was on the IANA Transition Coordination Group with me, and we often had similar positions on specific issues. On the question of China’s future contribution, I praised the efforts of Professor Xu Peixi to run lectures, workshops and schools that build up knowledge in China about the transnational environment of Internet governance and giving their people the knowledge and confidence to participate in global IG institutions. I also encouraged Chinese participants in GAC and other parts of the regime to help China send stronger signals that they accept and value Internet institutions involving nonstate actors. It would not be good faith to participate in the ICANN environment while working at cross purposes in multi-lateral institutions.
Many Chinese Internet techies are still interested in whether China can get a root server. The technical barriers to integrating additional root servers into the ICANN root no longer exist. There are some valid reasons for adding such a root server, such as reduced latency in answering queries. However, the Chinese I spoke with are pessimistic about whether this will happen. They think ICANN will never agree to place a root server in China because “they don’t like China.” To be sure, China’s promotion of a sovereigntist approach to internet governance is legitimate cause to be wary; as some in the Western Internet community seem to fear that a Chinese root server could become the basis for an alternate root. But it is the uniform content of the root zone file, not the presence of a root name server, that holds the DNS together. So far there is no indication that China wants to usurp ICANN’s status as editor of the root zone. Indeed, if it wanted to do that it wouldn’t need an official root server in the ICANN system; it could just set up an alternate root and see who else in the world would use it. A more interesting question we discussed is whether a Chinese root server would sit inside or outside the Great Firewall.
Flogging Facebook
Chinese students and intellectuals were fascinated by the recent Facebook breach and the ongoing controversies in the U.S. about Russian influence operations via social media. Americans might want to temper their outrage at Facebook by contemplating the fact that Chinese officials use the drama as confirmation of their belief that foreign social media in particular – and the internet in general – must be banned or heavily regulated to protect users and their own national security. These prejudices are reinforced by Westerners paid to write China Daily columns, like Philip J Cunningham, who provides a classic example of how seemingly progressive attacks on big tech can be used to rationalize censorship and authoritarianism. I was asked how I thought FB and other social media influence politics. I expressed the opinion that the influence of Russia on U.S. politics via Facebook was being exaggerated due to partisan shock at Trump’s election. All new media affect public opinion and political expression, but in complex ways. The strongest effects come from the way new media technologies and processes redistribute relative communicative capabilities among different groups. Those who take advantage of their new capabilities first are empowered in relation to those who don’t (e.g., the use of printing by Protestants in their competition with Catholics). I reminded them that not too long ago Facebook and other social media were being attacked because of liberal bias in the moderation of the newsfeed. As for the Cambridge Analytica abuse, it’s bad that Facebook didn’t monitor this more closely but they will suffer in the market for this. Standard liability and contract law can handle the question of who gets paid damages.
Asking about Attribution
There was some interest in the issue of attribution. I was asked by a government think tank whether it was acceptable to attribute a cyberattack based primarily on who was presumed to be the primary beneficiary of the attack. I was not sure what they meant by this. Evidently China feels uncomfortable, if not threatened, by such an approach. My answer affirmed that currently attribution is primarily a political game which is not well organized or transparent because it is performed by states. This is why we are supportive of the idea of a neutral International Attribution Organization (IAO) rooted in nonstate actors. The questioner expressed some skepticism about the Microsoft IAO proposal because of its source in a U.S. company. We explained why the interests of Microsoft and the U.S. government diverge sharply when it comes to attribution, so it would be a mistake to view Microsoft as an agent of the U.S. and reject the idea for that reason. However, we also recognize that an IAO would need support and backing from a much broader constituency if it was to win trust and achieve neutrality.
Cloudy skies for trade
I asked why China put foreign ownership restrictions on cloud services based in China. Recently Apple, Amazon and other American cloud companies have sold off their cloud facilities in China and entered into joint ventures with Chinese operators. Once again, the Facebook leaks were invoked. This is why we don’t believe foreign companies “could protect our data well,” they said. They trust local companies more. More generally, basic information infrastructure facilities in China must be state-owned and only value-added services can be foreign-owned. In the past, cloud was probably considered a value-added service. This has been a bedrock policy, rooted in sovereignty concerns, throughout the telecommunications liberalization of the 1990s. Post-Snowden, I inferred, data and cloud infrastructure seemingly is being re-classified (informally) as basic infrastructure.
Many in U.S. industry claim that Chinese investment and trade restrictions, which require joint ventures with local partners, force them to give away valuable intellectual property to their JV partner. I asked whether this was true. The answers provided did not show an awareness of the relationship between IPR transfers and foreign investment restrictions. One think tank said that when companies come to such a huge market it will help them to innovate. They also claimed that IPR protection in China is getting better, in part because younger Chinese are IPR creators so they need to protect it.
IPv6 migration
China’s level of migration to the new IPv6 protocol is near the bottom of world rankings. This is surprising because China’s gigantic Internet market would seem to be one of the prime beneficiaries of an expanded IP address space. Among the people we talked with, there was general agreement that China’s three big state-owned network infrastructure providers – China Telecom, China Mobile and China Unicom – are the reason for the lack of change. These sluggish SOEs, I was told, “got rich on IPv4 and are not eager to change.” China’s network infrastructure relies heavily on NAT (network address translation, by which a single global IPv4 address serves multiple users). Moving to IPv6 will be expensive for them and will bring no countervailing revenue enhancements.
Among policy makers who are not technical experts, there was some confusion about the impact of IPv6 on surveillance. The SOEs have been telling policy makers that if China converts to v6 “resources will be lost” and that terrorists can use IPv6 because it can be encrypted. In fact, as far as we can tell there is no change in the status of encryption between v4 and v6. On the other hand, as one local expert pointed out, by eliminating NAT IPv6 permits a more granular tracking of users. If unique global addresses can be assigned to every device the network is more transparent and law enforcement can identify who is doing what on the network more easily.
In November of last year, China adopted a national IPv6 migration plan initiated by the CAC and signed by President Xi Jinping. We are in the process of translating this document into English. Based on second-hand accounts, the plan will require the telecom SOEs to stop using NAT by the end of this year. Less clearly, we were told that the plan is supposed to stop buying of IPv4 addresses. If both NAT and IPv4 address acquisition are banned China will be in trouble. Migrating to IPv6 requires running both protocols until such time as there are so few IPv4 users that it can be turned off. That will take a while. In the meantime, continued use of IPv4 without NAT requires a growing number of IPv4 addresses. Either the IPv4 address space can be expanded by NAT or it can be expanded by buying additional numbers in the secondary market. There is no other alternative. Tunneling is not, as far as I know, a viable alternative.
Visiting the “Great Wall”
I turned down an offer to visit the Great Wall in the countryside, but in China one cannot avoid the Great Firewall. This was my first experience of the Chinese Internet in some time. (The ICANN 2013 meeting had unrestricted Internet access.) I was able to access the Georgia Tech Microsoft cloud with all my documents via hotel WiFi, but of course Google and all its applications are blocked. So is Twitter, and so are Telegram and WhatsApp (because they encrypt messages).
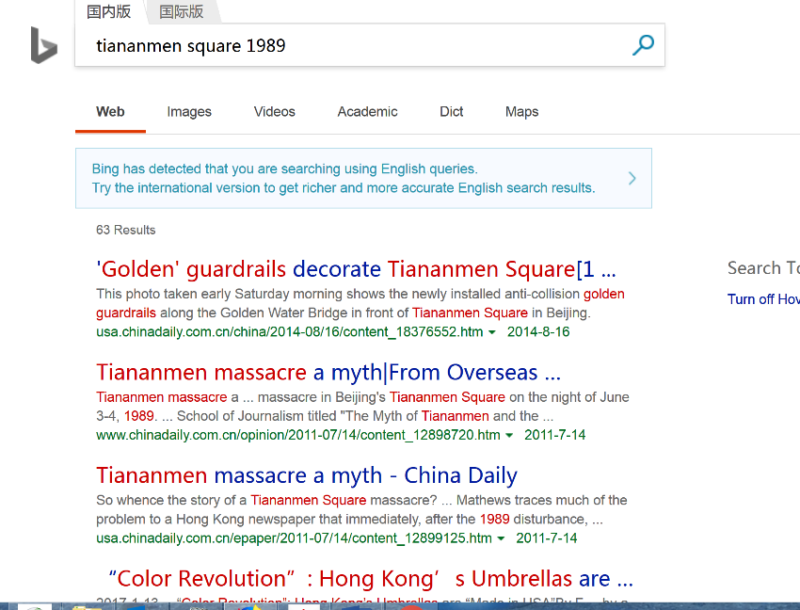 I had signed up for WeChat, the leading Chinese messaging service in China, to communicate with locals easily. Normally a WhatsApp user, I had to turn off Wifi to use it. It is blocked in China because it encrypts all chat messages. Georgia Tech’s VPN was not blocked, however, and got me through the firewall from my laptop as needed. I noticed that while Google’s search engine was blocked Microsoft’s Bing was not. When I inquired why this was the case, I was told that foreign companies have to comply with local laws; Microsoft does and Google doesn’t. After this I verified that Bing imposes a mandatory “safe search” (no porn) setting when accessed from China, and a search (in English) for “Tiananmen Square 1989” in Bing produced mainly articles from China’s state media claiming the Tiananmen massacre was a myth. Searching (in English) with Bing from a VPN, on the other hand, made Wikipedia’s page on the Tiananmen Square incident the top result and provided links to a number of news reports and critical accounts of the fateful 1989 clash in the center of Beijing. So Microsoft does not merely filter out articles objectionable to the Chinese state, it seems to actively elevate and promote state-approved propaganda on such topics.
I had signed up for WeChat, the leading Chinese messaging service in China, to communicate with locals easily. Normally a WhatsApp user, I had to turn off Wifi to use it. It is blocked in China because it encrypts all chat messages. Georgia Tech’s VPN was not blocked, however, and got me through the firewall from my laptop as needed. I noticed that while Google’s search engine was blocked Microsoft’s Bing was not. When I inquired why this was the case, I was told that foreign companies have to comply with local laws; Microsoft does and Google doesn’t. After this I verified that Bing imposes a mandatory “safe search” (no porn) setting when accessed from China, and a search (in English) for “Tiananmen Square 1989” in Bing produced mainly articles from China’s state media claiming the Tiananmen massacre was a myth. Searching (in English) with Bing from a VPN, on the other hand, made Wikipedia’s page on the Tiananmen Square incident the top result and provided links to a number of news reports and critical accounts of the fateful 1989 clash in the center of Beijing. So Microsoft does not merely filter out articles objectionable to the Chinese state, it seems to actively elevate and promote state-approved propaganda on such topics.
Concluding observations
One overarching observation is that most of the Chinese people I met are fully acclimated to a more authoritarian, paternalistic system of government. Even when they chafe at, say, the pettiness of the Great Firewall’s restrictions on this or that, none of them I met have a revolutionary or rebellious attitude towards it. A vivid example of this, unrelated to Internet governance, was provided by many of the people I dined or drank with. Without exception, anyone driving a car refused to take a single sip of alcohol, no matter how little, and regardless of how much time would pass before the driving was to take place. This was because Beijing has adopted extremely strict penalties for driving under the influence. The people I met were not making any risk-reward calculations, they were just complying fully with the law as a matter of course. Indeed, the regulations have created a small industry of guys who can be hired to drive you home if you are drunk; they hang around in clusters on street corners in uniforms and electric bikes ready to speed off to a customer at a moment’s notice.
I deliberately chose an example in which the effects of such obedience are obviously beneficial. But I also asked about Xi Jinping’s end of term limits and found little concern about it. China needs continuity and stability at this time, I was told. At one university there were a few sardonic comments about it, but that was all.
The good news is that China’s students and intellectuals are eager to become more integrated into global Internet governance communities and discussions. Although language is the biggest barrier, this needs to happen, and is happening. Many thanks to my amazing hosts!

Congrats for the invitation – and thanks for the detailed report.
Norbert
Kep/Cambodia
Dear Milton,
Thank you for this truly excellent report. I agree with almost all of your analysis and my knowledge of China is consistent with everything you report. However, I do take issue with some specific statements that you make in the first section, titled “Multistakeholder …” .
1) You state: “A better approach is to confine multilateral governance to areas where it cannot be avoided, such as in military or trade negotiations, …”
Why should trade negotiations be purely multilateral? OK, customs duties are the prerogative of states, but why shouldn’t they consult the concerned parties, namely industry and consumers? And guess what, they do (at least for what concerns industry), but only at the national level. Why shouldn’t the concerned parties be involved also at the international level?
And this in particular when, as is the case at present, trade negotiations aren’t really about trade, they are about what to deregulate at the national level. And, in the e-commerce agenda, about spam, e-signature, free flow of data, prohibiting procurement of open source software, and other issues which have nothing to do with trade properly speaking.
Even for military matters, all parties should be consulted. And note that “security” is often viewed as part of “military”, and surely you are not implying that all parties should not be consulted with respect to Internet security matter.
2) You state: “Multilateral governance, in contrast, eliminates everyone but governments. Multistakeholder governance is therefore more likely to incorporate viewpoints and knowledge that will be needed to develop and understand the effects of policies.”
As you know, the first sentence is correct only for WTO and free trade negotiations. Other intergovernmental forums, such as ITU, UN, WIPO, do allow participation by non-state actors, even if decisions are finally made by governments. So, apart from WTO and trade negotiations, multilateral governance does allow opportunities to incorporate viewpoints and knowledge of non-state actors.
So the question is not one of principle, but one of effectiveness: which model is more likely to give an effective voice to non-state actors? I submit that, as usual, the devil is in the details, so the answer depends on the specific organization and the specific topic being discussed. For example, decisions in the ITU Radio Sector are heavily influenced by industry, as they should be.
Further, governments are supposed to act in the interests of their citizens. So they are supposed to conduct consultations before making decisions. And in fact many countries do that, in some way or another. As you know, in Switzerland the government goes to extremes to consult all parties before making decisions, because many decisions can be challenged by referendum. Even if not all countries conduct consultations as extensively as does Switzerland, I still think that it inappropriate to pretend that government representatives in multilateral organizations take positions on their own without any reference to national consultations.
On the other hand, I do find that in some countries (including the USA), the national consultations are not always adequate (e.g. for copyright matters), so the government’s positions may not really reflect the popular will. But that’s a failure at the national level, and I fear that it would be replicated at the international level.
Let’s take copyright as an example. Would the copyright lobby be weaker if WIPO were organized along the lines of ICANN? Surely not: the copyright lobby would be even stronger than it is in the current WIPO. (In fact, as you know, TRIPS was negotiated in WTO precisely because the patent lobby couldn’t get what it wanted out of WIPO, and the copyright lobby managed to get their wishes into TRIPS.)
So, while I would agree that WTO is a great example of a dysfunctional intergovernmental organization, I would not agree that all intergovernmental organizations are dysfunctional and I would not agree that no Internet governance issue should ever be discussed in an intergovernmental organization. I would agree that all intergovernmental organizations should be more open to participation by non-state actors.
And I believe that it is imperative to prevent WTO (and trade negotiations) from discussing Internet governance matters.
3) You refer to “transnational non-state actors “. There are of course many transnational non-governmental organizations, but most of them have purely advocacy roles (e.g. ISOC, or Human Rights Watch, or whatever). A few have governance roles, e.g. Red Cross, IATA. But the only one that I can think of that has a governance role (I’m distinguishing governance from standards-making) and that does not operate within the framework of some sort of formal intergovernmental agreement, is ICANN. Are there any other examples of a transnational non-state actor that has a governance/regulatory role and that does not operate under a formal intergovernmental agreement?
Apart from the above, I fully agree with your article.
Best,
Richard
thank you Professor Mueller for giving the lectures and sharing the insights!
wel written !! interestingly wicked !!