I’ve recently returned from the Cybersecurity and Cyberconflict: State of the Art Research Conference, organized by Dr. Myriam Dunn Cavelty and her colleagues at the Center for Security Studies, ETH, in Zürich, Switzerland. The conference brought together a mix of scholars researching “the strategic (mis)use of cyberspace by state and non-state actors and…analysing the related governance challenges.” In addition to our own work on public attribution of state-sponsored cyber attacks, a wide range of intriguing research was presented. This included, but was not limited to, networked governance and Science and Technology Studies (STS) research on public and private threat intelligence actors, numerous country-level case studies including a discouraging assessment of Ukraine’s intergovernmental supported effort to improve it’s cyber and information security, and analyses of the U.S. Government’s strategic shift to cyber offense as well as its recently announced Cyber Deterrence Initiative. In this post, I’ll highlight some of the main points from the research we presented and, where appropriate, interweave comments received and other relevant work presented.
Our draft paper, Understanding transnational cyber-attribution: Moving from “whodunit” to who did it, explored the process of attribution of state-sponsored attacks and the incentives to make an attribution or not. We started by analyzing a subset of the Council on Foreign Relations’ Cyber Operation Trackers dataset, including 82 incidents from 2016 to the 1Q of 2018, supplemented with additional information on who and how public attributions were made. While we recognize the limitations of the data (as did our colleagues in Zürich), sometimes you need to approach research pragmatically. We think several useful initial observations can be made.
First, the vast majority of incidents (70, or 85%) resulted in some form of public attribution, with only 12 incidents (15%) not being attributed to a perpetrator. A small number of incidents, 7 (9%), included attributions involving both government(s) and private actor(s). These public attributions may have involved coordinated action between states (e.g., NotPetya) or states and non-state actors (e.g., WannaCry), or attributions published by non-state actors citing anonymous government sources, or what appeared to be separate attributions made independently by private actors and states (e.g., Democratic National Committee hacks). While governments made 18% (15) of the attributions, the largest number of attributions have been made by private actors (48, or 58%), a category that includes threat intelligence organizations, network security companies and news media organizations. The importance of private actors in attribution is evident from the number of attributions made by them, which seems to be nearly doubling over the past three years. It also highlights the need for institutionalizing the attribution process which includes forensic, legal, and political aspects.
The re-coded incident data also allowed us to make important distinctions. Table 2 (below) shows attributions made to threat group(s) or state sponsor(s) by the actor type making the attribution. The total number of attributions made differs from the number of incidents as more than one entity may be implicated per incident by one or more actor type. Again, private actors are making the most attributions to both threat groups and/or states.
Table 2: Attributions made by actor type to actor type
| Attribution made by (actor type) | Incidents attributed to threat group | Incidents attributed to state sponsor |
|---|---|---|
| Both government(s) and private actor(s) | 4 | 7 |
| Government(s) | 5 | 13 |
| Private actor(s) | 31 | 38 |
| Grand Total | 40 | 58 |
Interestingly, despite the appearance that states may be more inclined to make attributions to other states, a Chi-Square test concludes there is no significant difference between actor type with regard to whom (threat group or state sponsor) they attribute incidents. Neither states nor private actors are more likely, or perhaps better suited, to make attributions to a specific type of actor. The paper goes on to look at how public attribution of state-sponsored attacks has been largely driven by evolving use of US legal and administrative procedures.
The next part of the study related the above data to some current game-theoretical modeling around when and how states engage in attribution. Here we found support for Edwards, et. al’s conclusion that it is rarely beneficial for an attacked state to independently increase its attribution capability, given that it’s not likely result in a stable outcome (e.g., no attacks). For example, to this day Ukraine still suffers attacks despite roundly blaming Russian actors, and similarly, the United States’ questionable forensic case, as well as indictment and sanctions against Russian operators for the DNC hacks has seemingly not resulted in deterring “information operations.” To the contrary, Edwards et al argue the likelihood of stable equilibrium(s) (i.e., no attack; attack, blame) increases if both attackers and victims become knowledgeable through improved symmetric technical attribution capabilities. Again the data support how collectively determined attribution methods and outcomes have evolved and arguably encourage restraint, but they also suffer from shortcomings as currently conceived.

This is illustrated by the WannaCry and NotPetya incidents which were followed by public attribution efforts coordinated between multiple allied states, and seemingly to a lesser degree, private actors. These processes are beginning to be institutionalized, with the Australian ministerial and communique expressing that the Five Eyes “would coordinate on appropriate responses and attribution” as well as the Cyber Deterrence Initiative (CDI) in the recently announced National Cyber Strategy by the United States. The CDI similarly proposes collective information sharing among, and public attribution from, “like-minded” partners. Although, as another researcher in Zürich noted, there are few details on how it actually works in practice. Moreover, the limited number of actors involved raises the question whether these attributions will be accepted more broadly. It also became clear in our discussions that this isn’t the only potential institutional response to the problem of attributing state-sponsored attacks. The role of epistemic communities, e.g., university-based attribution, was raised, as well as indications that the cyber insurance market may also have strong economic incentives to perform attribution of these types of attacks.
IGP maintains that there is a need for more interdisciplinary research on institutionalizing transnational attribution processes. While a handful of proposals have been made (which we reviewed in our recent white paper), these and more general existing frameworks (e.g., technical, international law) appear inadequate to explain how institutionalization might occur. We are only just beginning to understand what these processes might look like and how they might work in practice, and the impact that they might have on all nation-states’ incentives to conduct cyber attacks.
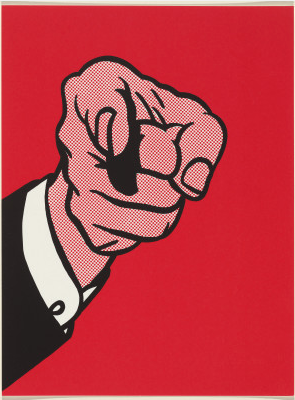
Featured image credit: Labrona, Untitled, (2016). Labrona is recognized as “one of the top one hundred street artists in the world“. His work can be found in many places, including this image which adorns an underpass in Toronto.
